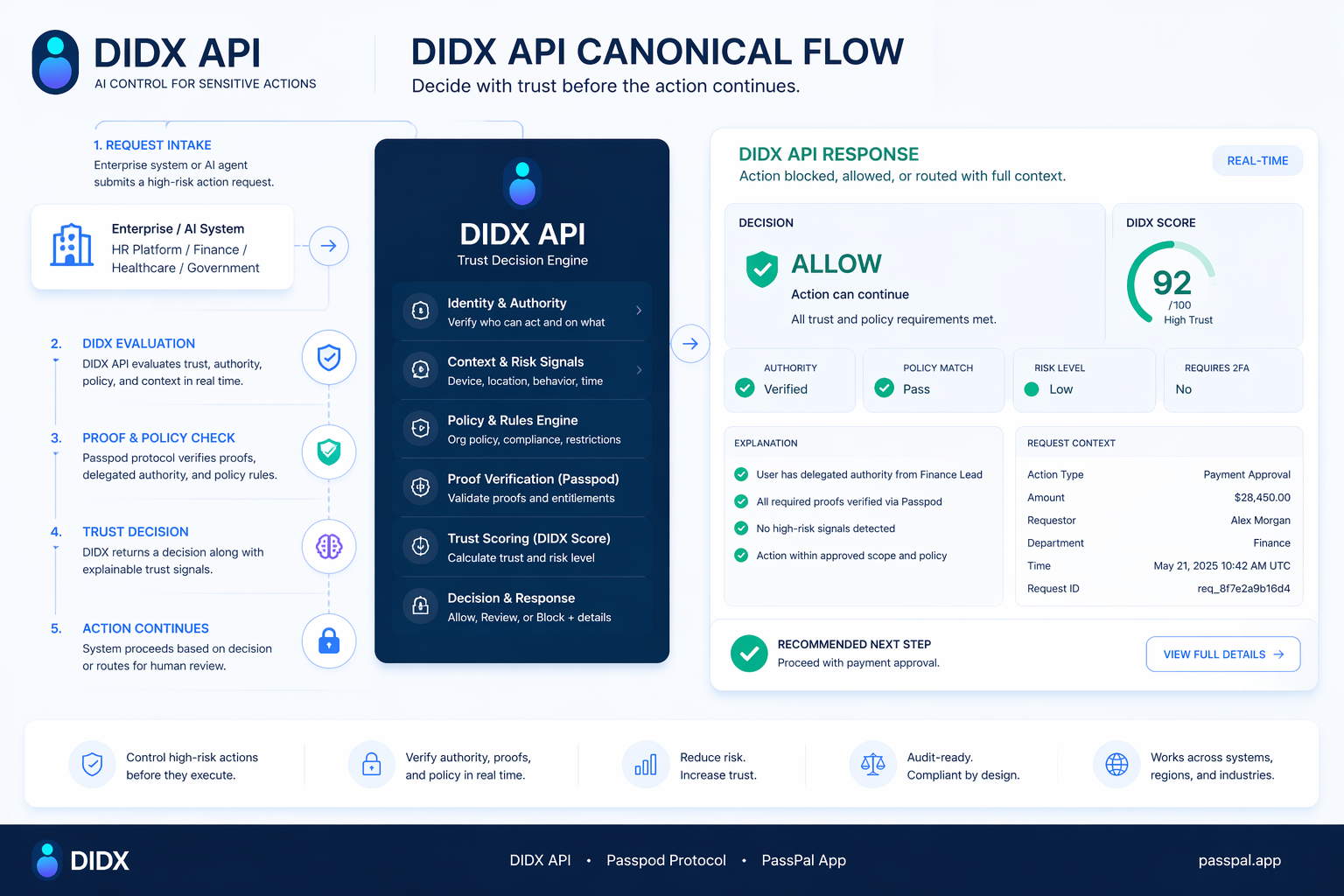
DIDX API
What the institution sees: a clean trust decision for authority, approvals, onboarding, recovery, or AI execution.
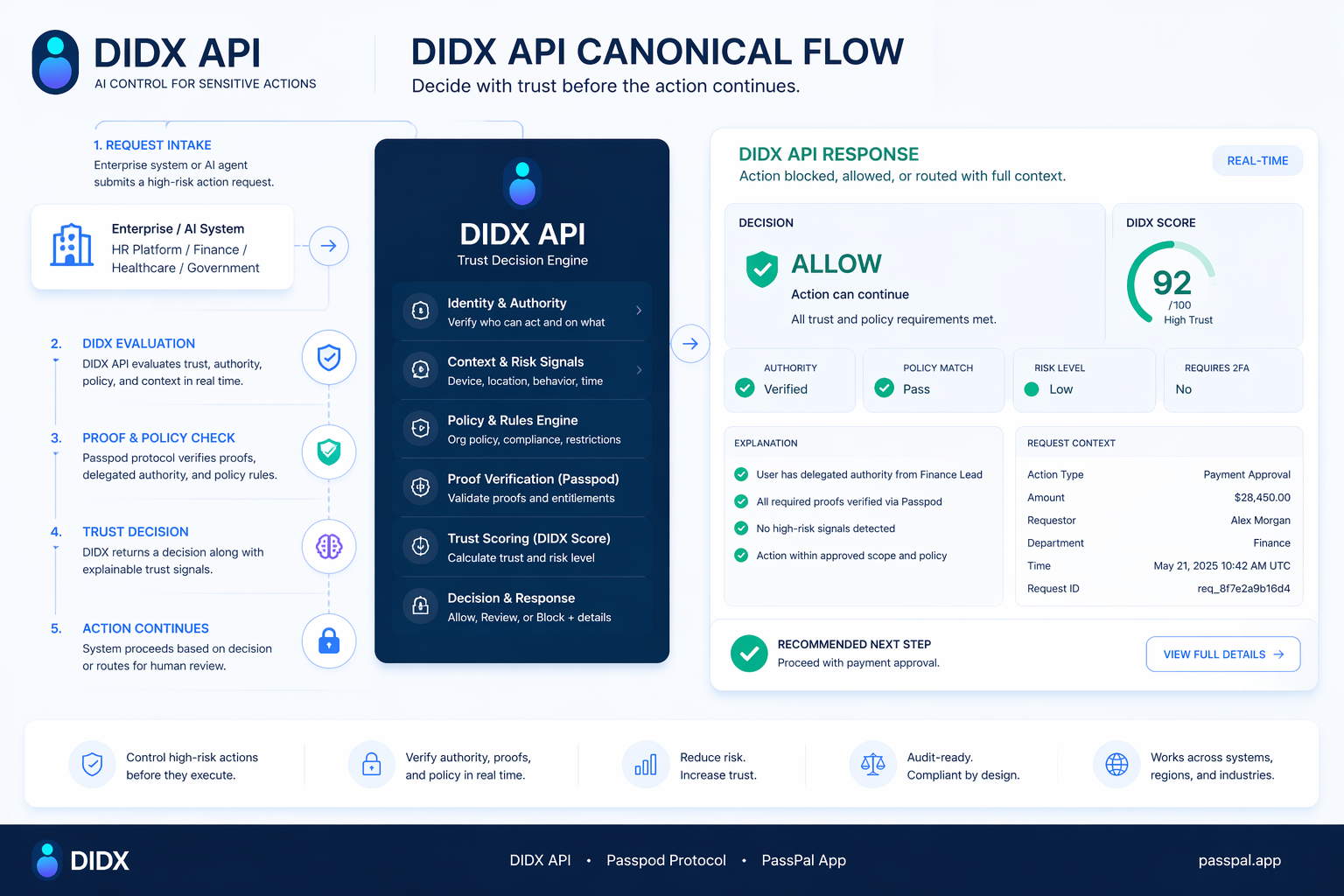
DIDX API gives enterprises a trust decision layer for high-risk actions. PassPal gives users the clean proof handoff. Passpod decides whether the action can continue.
One trust layer. Two interfaces. The enterprise gets a clean decision. The user gets a clean request. The action only moves forward if the right conditions exist.
Trust? Proven! — but only for the action that matters, at the moment it matters.

DIDX API is the enterprise decision surface. PassPal is the user proof handoff. The model only works when both sides stay visible.
What the institution sees: a clean trust decision for authority, approvals, onboarding, recovery, or AI execution.
What the user sees: a readable request, the right proof level, and the next clear step — without oversharing.

DIDX Enterprise does not just verify identity or attributes. It decides whether a sensitive human or AI action should be allowed to continue at all.
The system must state what it wants to do, for whom, in which workflow, and why. No structured intent, no sensitive execution.
The request is classified as approval, payment, onboarding, recovery, access, disclosure, or admin change and gets a trust threshold.
The user sees a plain-language request and can approve, narrow scope, deny, escalate, or stop the path before the action executes.
The target system only accepts the action if a valid pass exists and runtime conditions still match. Revocation stays possible.
Start with sensitive workflows where DIDX API and PassPal can turn scattered proof, authority, and risk signals into a clearer decision.
Verify whether someone can legally act for an organization for this exact action, not in general.
The real enterprise question is not only who the person is. It is whether they can do this exact action right now.
Confirm that a payment, contract, or approval comes from the right person with the right authority.
This is the easiest monetization path because companies already understand weak approval chains and unsafe execution risk.
Protect high-risk resets and recovery flows from phishing, persuasion, help-desk abuse, and unsafe AI-assisted actions.
Recovery UX must feel safe without becoming a dead end. Weak fallback logic kills trust fast.
Verify that a vendor-side contact is the real, current, authorized representative before money or access moves.
It gets much better when legal-entity names and role freshness are clean. Otherwise too many cases drift into manual review.
Move onboarding forward with only the verified attributes needed for the decision, not a document dump ritual.
Users feel the privacy win immediately: less oversharing, less friction, more transparency.
Weak shortcuts on one side. Action-bound trust control on the other.
Use DIDX API as the enterprise trust decision layer for workflows where people and systems need a cleaner answer before the action continues.
The strongest story is simple: this is not more identity friction. It is a clearer way to stop sensitive human and AI actions unless the right proof and approval are in place.